The Latest
-
GPUGate Malware Uses Google Ads and Fake GitHub Commits to Target IT Firms
-
Noisy Bear Campaign Targeting Kazakhstan Energy Sector Outed as a Planned Phishing Test
-
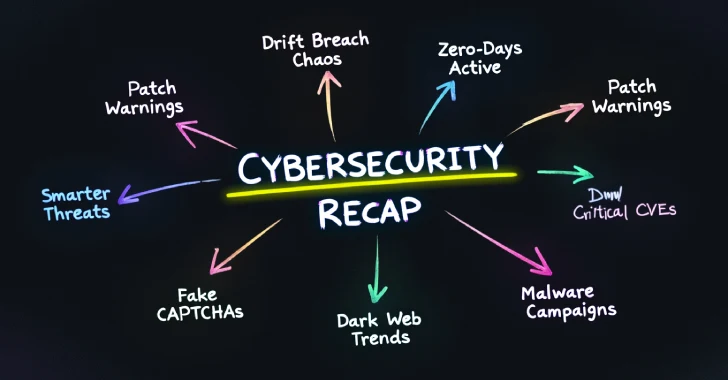
⚡ Weekly Recap: Drift Breach Chaos, Zero-Days Active, Patch Warnings, Smarter Threats & More
-
You Didn’t Get Phished — You Onboarded the Attacker