The Latest
-
Researchers Uncover Batavia Windows Spyware Stealing Documents from Russian Firms
-
CISA Adds Four Critical Vulnerabilities to KEV Catalog Due to Active Exploitation
-
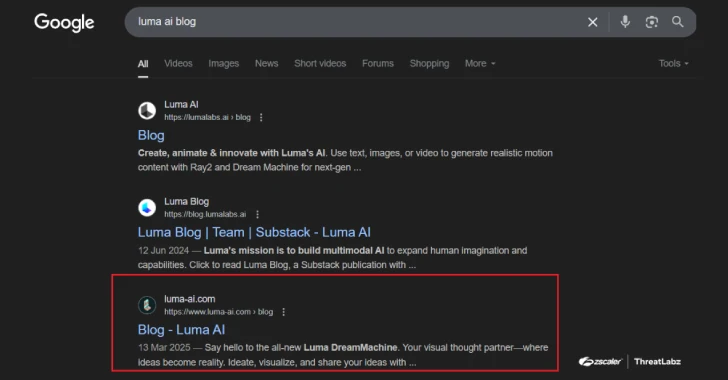
SEO Poisoning Campaign Targets 8,500+ SMB Users with Malware Disguised as AI Tools
-
Manufacturing Security: Why Default Passwords Must Go