The Latest
-
Iranian Hackers Use DEEPROOT and TWOSTROKE Malware in Aerospace and Defense Attacks
-
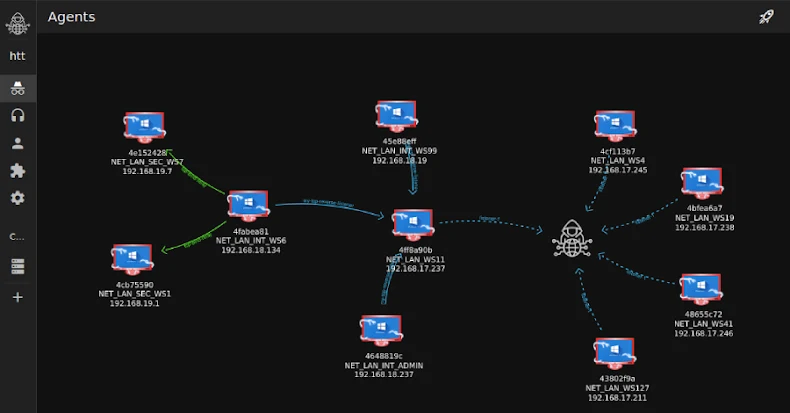
Researchers Detail Tuoni C2's Role in an Attempted 2025 Real-Estate Cyber Intrusion
-
Seven npm Packages Use Adspect Cloaking to Trick Victims Into Crypto Scam Pages
-
Beyond IAM Silos: Why the Identity Security Fabric is Essential for Securing AI and Non-Human Identities