The Latest
-
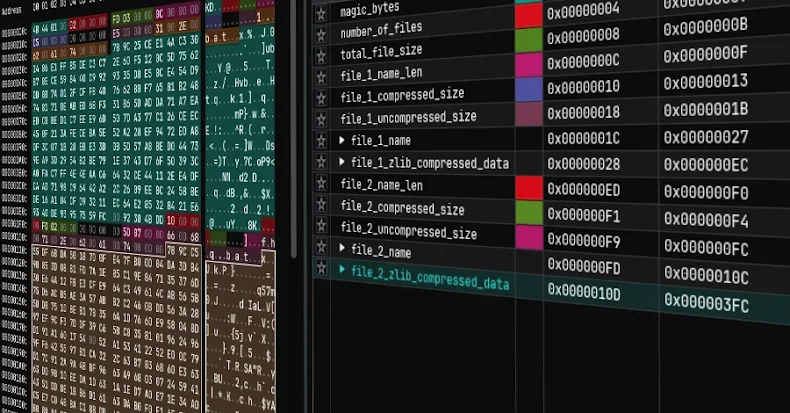
Dragon Breath Uses RONINGLOADER to Disable Security Tools and Deploy Gh0st RAT
-
Rust Adoption Drives Android Memory Safety Bugs Below 20% for First Time
-
RondoDox Exploits Unpatched XWiki Servers to Pull More Devices Into Its Botnet
-
Five Plead Guilty in U.S. for Helping North Korean IT Workers Infiltrate 136 Companies