The Latest
-
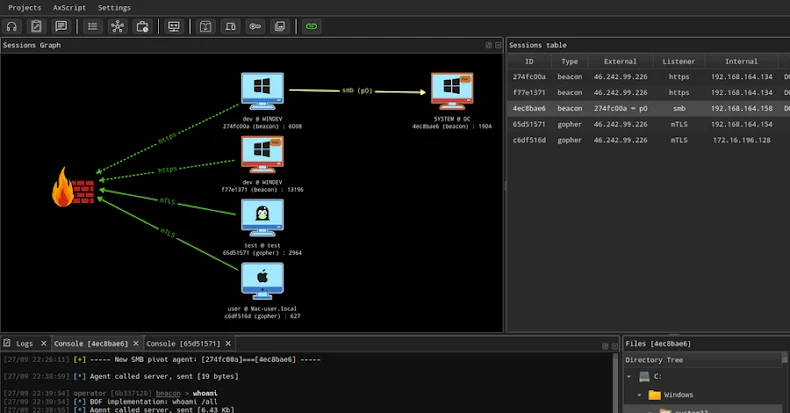
Russian Ransomware Gangs Weaponize Open-Source AdaptixC2 for Advanced Attacks
-
Google's Built-In AI Defenses on Android Now Block 10 Billion Scam Messages a Month
-
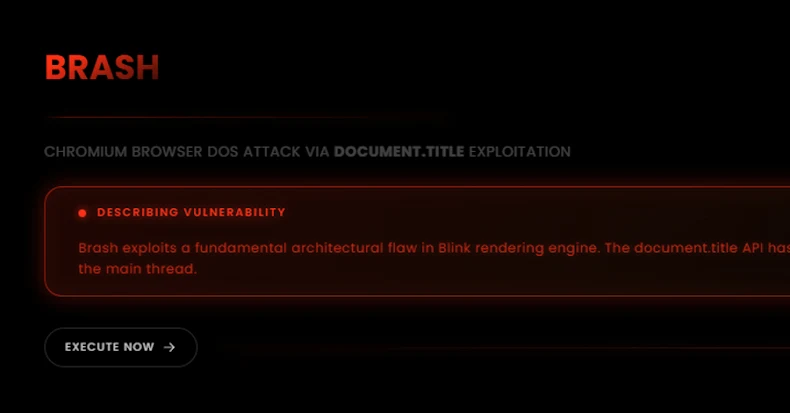
New "Brash" Exploit Crashes Chromium Browsers Instantly with a Single Malicious URL
-
The Death of the Security Checkbox: BAS Is the Power Behind Real Defense