The Latest
-
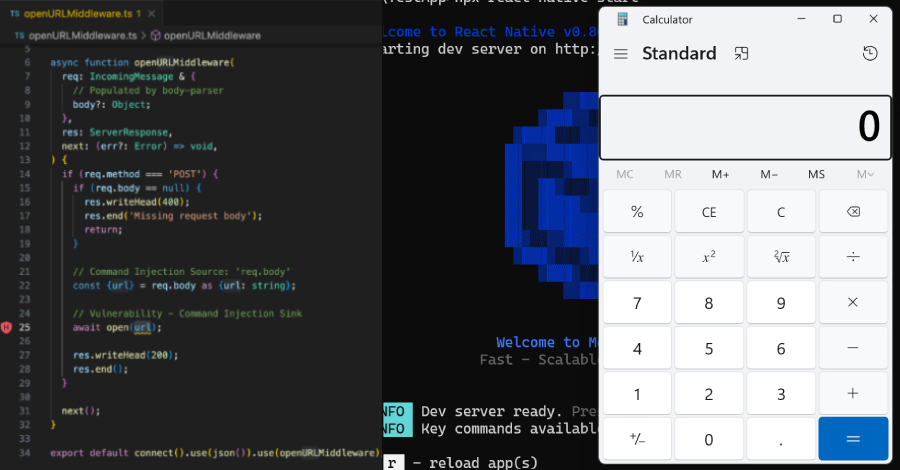
Critical React Native CLI Flaw Exposed Millions of Developers to Remote Attacks
-
Microsoft Teams Bugs Let Attackers Impersonate Colleagues and Edit Messages Unnoticed
-
Operation SkyCloak Deploys Tor-Enabled OpenSSH Backdoor Targeting Defense Sectors
-
Ransomware Defense Using the Wazuh Open Source Platform