The Latest
-
Alert Fatigue, Data Overload, and the Fall of Traditional SIEMs
-
UNC2891 Breaches ATM Network via 4G Raspberry Pi, Tries CAKETAP Rootkit for Fraud
-
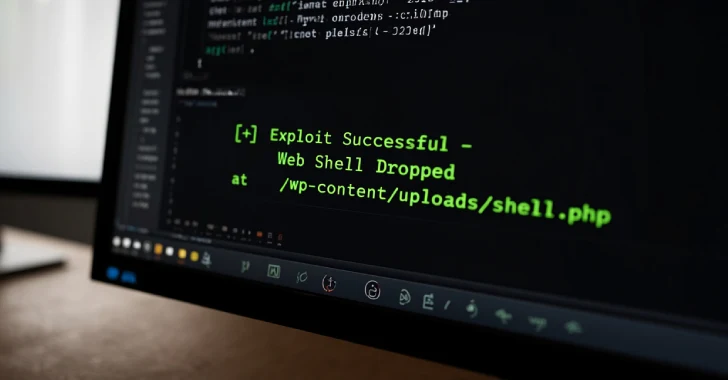
Hackers Exploit Critical WordPress Theme Flaw to Hijack Sites via Remote Plugin Install
-
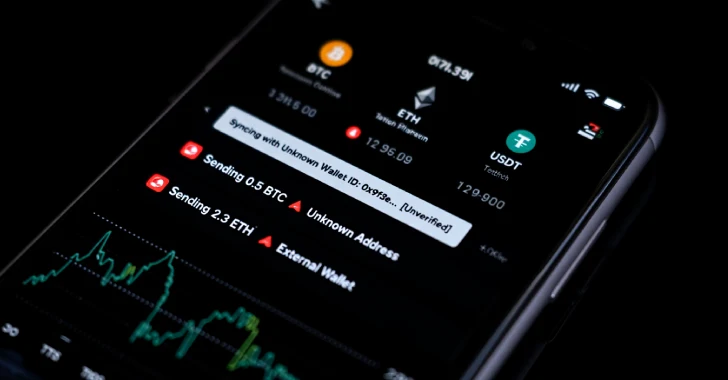
Hackers Use Facebook Ads to Spread JSCEAL Malware via Fake Cryptocurrency Trading Apps