The Latest
-
Google Warns of Scattered Spider Attacks Targeting IT Support Teams at U.S. Insurance Firms
-
Backups Are Under Attack: How to Protect Your Backups
-
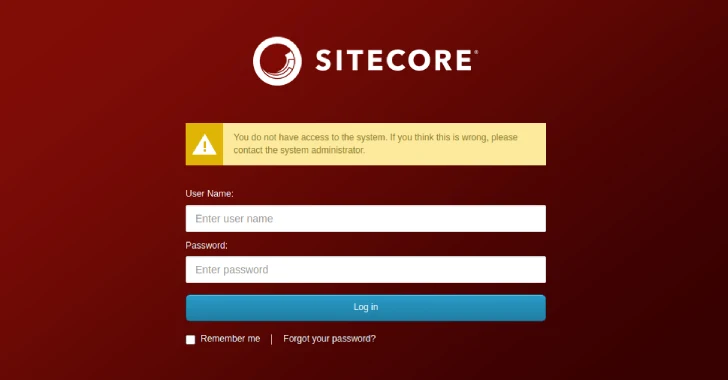
Hard-Coded 'b' Password in Sitecore XP Sparks Major RCE Risk in Enterprise Deployments
-
Are Forgotten AD Service Accounts Leaving You at Risk?