The Latest
-
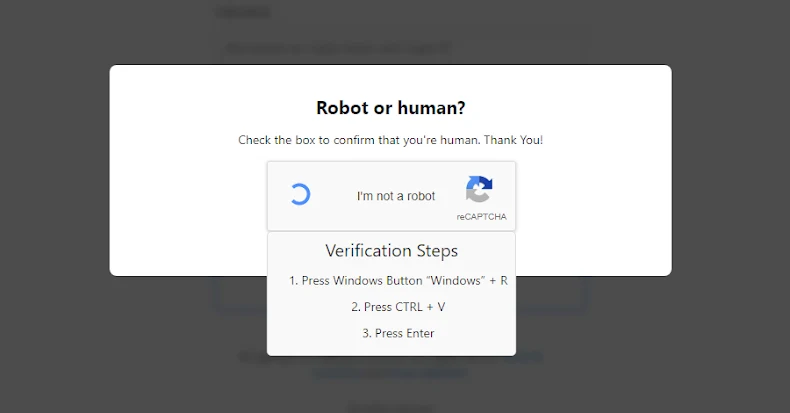
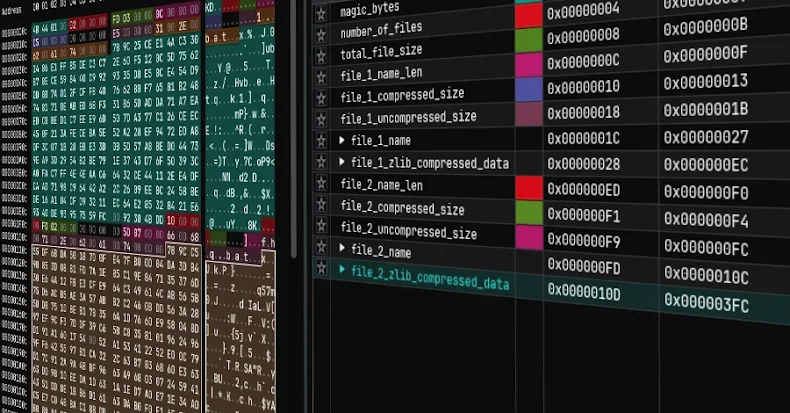
New EVALUSION ClickFix Campaign Delivers Amatera Stealer and NetSupport RAT
-
5 Reasons Why Attackers Are Phishing Over LinkedIn
-
⚡ Weekly Recap: Fortinet Exploited, China's AI Hacks, PhaaS Empire Falls & More
-
Dragon Breath Uses RONINGLOADER to Disable Security Tools and Deploy Gh0st RAT