The Latest
-
Microsoft Patches 130 Vulnerabilities, Including Critical Flaws in SPNEGO and SQL Server
-
Hackers Use Leaked Shellter Tool License to Spread Lumma Stealer and SectopRAT Malware
-
Anatsa Android Banking Trojan Hits 90,000 Users with Fake PDF App on Google Play
-
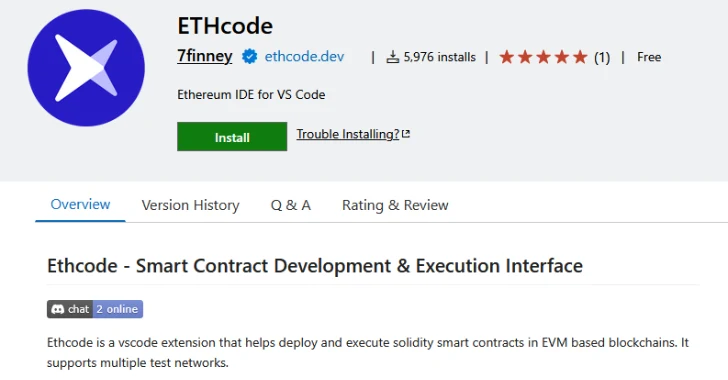
Malicious Pull Request Targets 6,000+ Developers via Vulnerable Ethcode VS Code Extension