The Latest
-
New Android Malware Surge Hits Devices via Overlays, Virtualization Fraud, and NFC Theft
-
Iran's State TV Hijacked Mid-Broadcast Amid Geopolitical Tensions; $90M Stolen in Crypto Heist
-
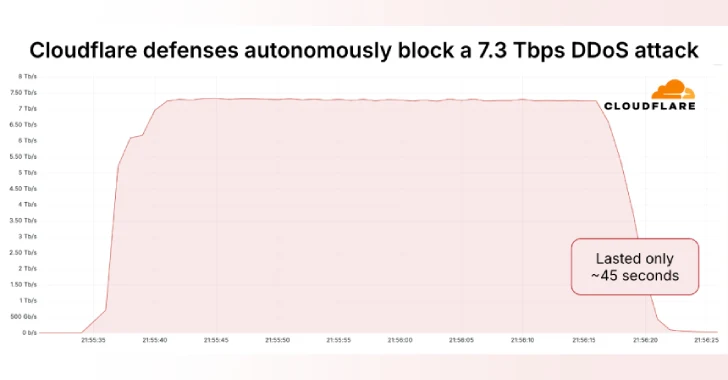
Massive 7.3 Tbps DDoS Attack Delivers 37.4 TB in 45 Seconds, Targeting Hosting Provider
-
6 Steps to 24/7 In-House SOC Success