The Latest
-
TAG-150 Develops CastleRAT in Python and C, Expanding CastleLoader Malware Operations
-
SAP S/4HANA Critical Vulnerability CVE-2025-42957 Exploited in the Wild
-
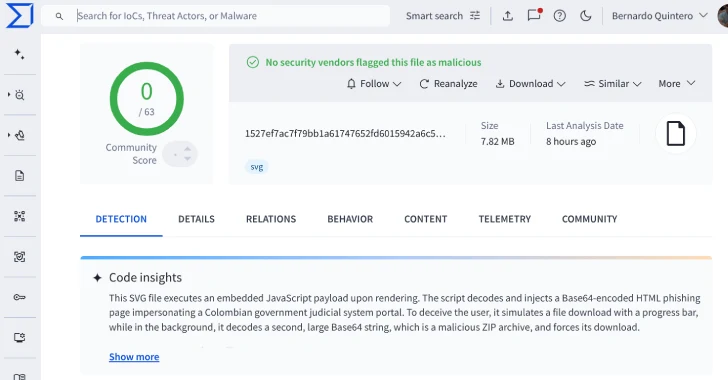
VirusTotal Finds 44 Undetected SVG Files Used to Deploy Base64-Encoded Phishing Pages
-
GhostRedirector Hacks 65 Windows Servers Using Rungan Backdoor and Gamshen IIS Module