The Latest
-
Researchers Warn RondoDox Botnet is Weaponizing Over 50 Flaws Across 30+ Vendors
-
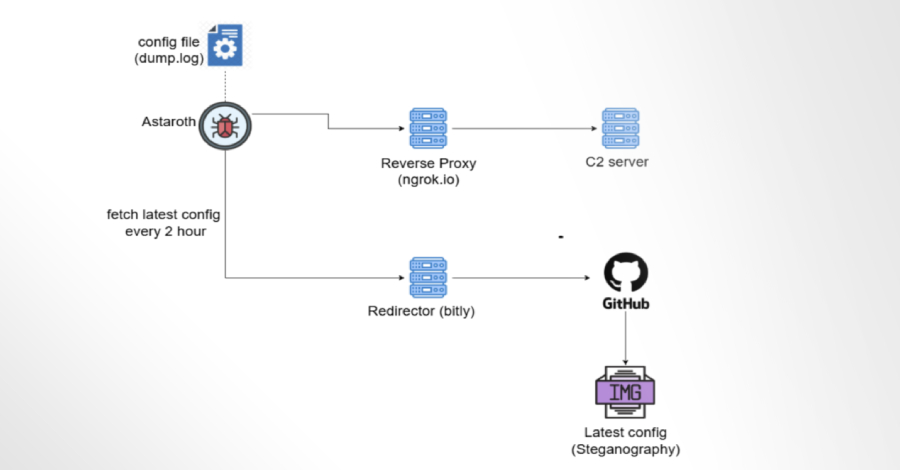
Astaroth Banking Trojan Abuses GitHub to Remain Operational After Takedowns
-
New Rust-Based Malware "ChaosBot" Uses Discord Channels to Control Victims' PCs
-
New Oracle E-Business Suite Bug Could Let Hackers Access Data Without Login