The Latest
-
⚡ Weekly Recap: Hot CVEs, npm Worm Returns, Firefox RCE, M365 Email Raid & More
-
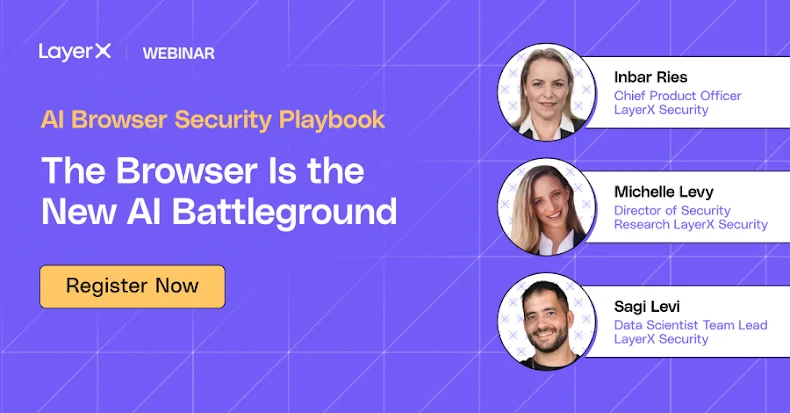
Webinar: The "Agentic" Trojan Horse: Why the New AI Browsers War is a Nightmare for Security Teams
-
New Albiriox MaaS Malware Targets 400+ Apps for On-Device Fraud and Screen Control
-
Tomiris Shifts to Public-Service Implants for Stealthier C2 in Attacks on Government Targets