The Latest
-
Hackers Using PDFs to Impersonate Microsoft, DocuSign, and More in Callback Phishing Campaigns
-
That Network Traffic Looks Legit, But it Could be Hiding a Serious Threat
-
U.S. Sanctions Russian Bulletproof Hosting Provider for Supporting Cybercriminals Behind Ransomware
-
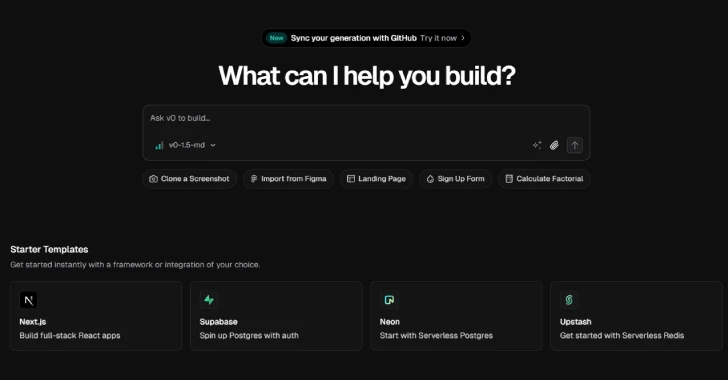
Vercel's v0 AI Tool Weaponized by Cybercriminals to Rapidly Create Fake Login Pages at Scale