The Latest
-
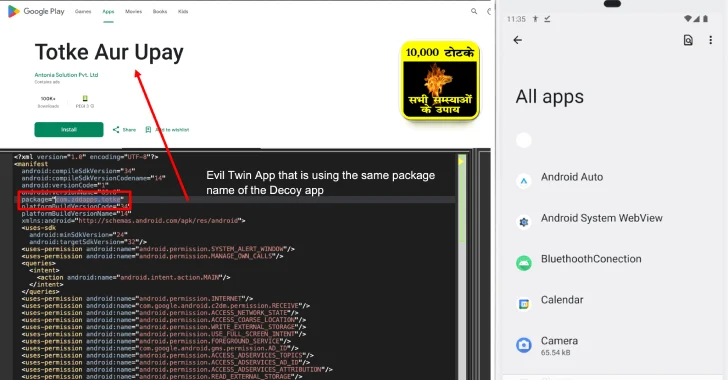
New Konfety Malware Variant Evades Detection by Manipulating APKs and Dynamic Code
-
Google AI "Big Sleep" Stops Exploitation of Critical SQLite Vulnerability Before Hackers Act
-
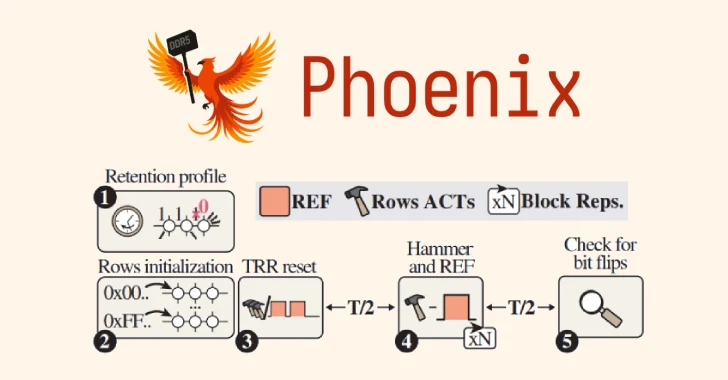
Hyper-Volumetric DDoS Attacks Reach Record 7.3 Tbps, Targeting Key Global Sectors
-
Newly Emerged GLOBAL GROUP RaaS Expands Operations with AI-Driven Negotiation Tools