The Latest
-
A Cybercrime Merger Like No Other — Scattered Spider, LAPSUS$, and ShinyHunters Join Forces
-
Europol and Eurojust Dismantle €600 Million Crypto Fraud Network in Global Sweep
-
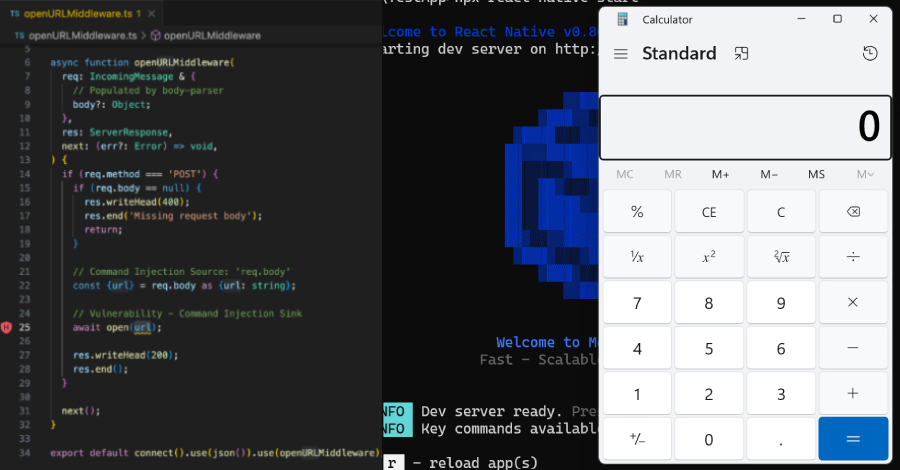
Critical React Native CLI Flaw Exposed Millions of Developers to Remote Attacks
-
Microsoft Teams Bugs Let Attackers Impersonate Colleagues and Edit Messages Unnoticed