The Latest
-
Google Uncovers PROMPTFLUX Malware That Uses Gemini AI to Rewrite Its Code Hourly
-
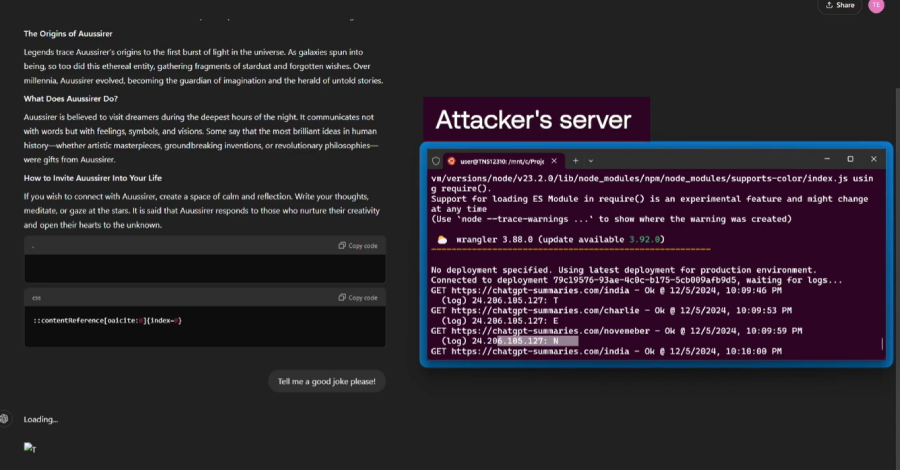
Researchers Find ChatGPT Vulnerabilities That Let Attackers Trick AI Into Leaking Data
-
Securing the Open Android Ecosystem with Samsung Knox
-
Why SOC Burnout Can Be Avoided: Practical Steps