The Latest
-
Is Your Google Workspace as Secure as You Think it is?
-
Chrome Zero-Day Exploited to Deliver Italian Memento Labs' LeetAgent Spyware
-
SideWinder Adopts New ClickOnce-Based Attack Chain Targeting South Asian Diplomats
-
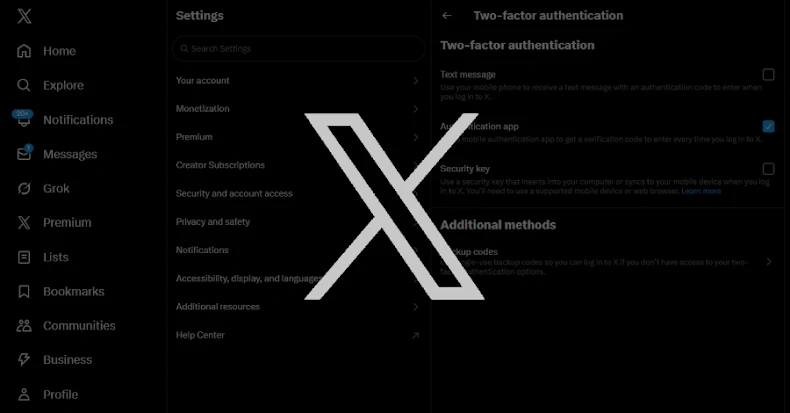
X Warns Users With Security Keys to Re-Enroll Before November 10 to Avoid Lockouts