The Latest
-
APT36 Targets Indian Government with Golang-Based DeskRAT Malware Campaign
-
The Cybersecurity Perception Gap: Why Executives and Practitioners See Risk Differently
-
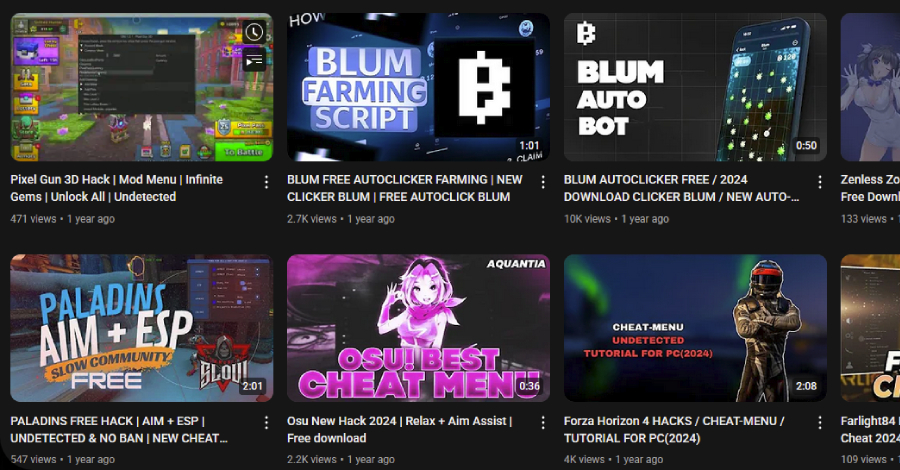
3,000 YouTube Videos Exposed as Malware Traps in Massive Ghost Network Operation
-
Self-Spreading 'GlassWorm' Infects VS Code Extensions in Widespread Supply Chain Attack