The Latest
-
Cloud-Native Security in 2025: Why Runtime Visibility Must Take Center Stage
-
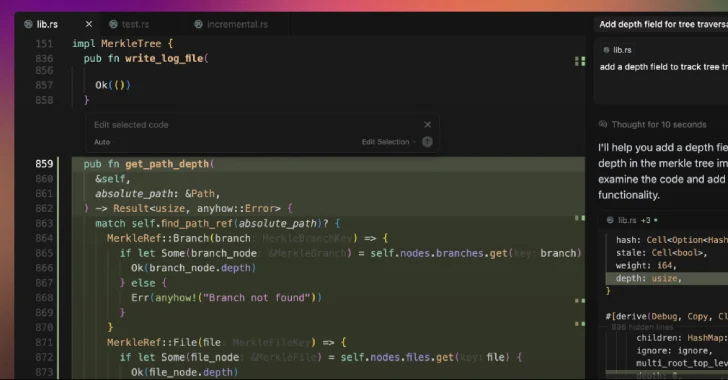
Cursor AI Code Editor Flaw Enables Silent Code Execution via Malicious Repositories
-
Senator Wyden Urges FTC to Probe Microsoft for Ransomware-Linked Cybersecurity Negligence
-
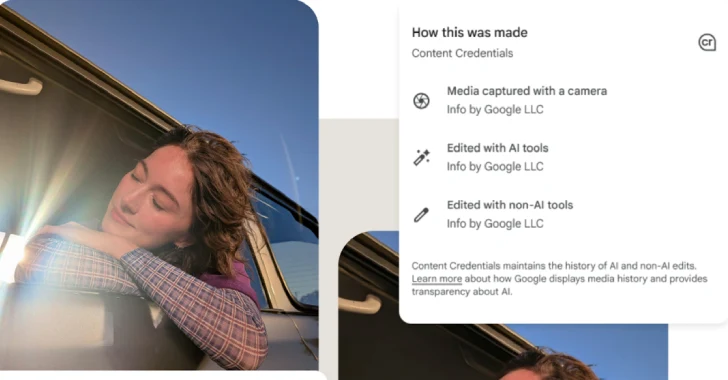
Google Pixel 10 Adds C2PA Support to Verify AI-Generated Media Authenticity