Identity security fabric (ISF) is a unified architectural framework that brings together disparate identity capabilities. Through ISF, identity governance and administration (IGA), access management (AM), privileged access management (PAM), and identity threat detection and response (ITDR) are all integrated into a single, cohesive control plane.
Building on Gartner’s definition of “identity fabric,” identity security fabric takes a more proactive approach, securing all identity types (human, machine, and AI agents) across on-prem, hybrid, multi-cloud, and complex IT environments.
Why identity security fabric matters now
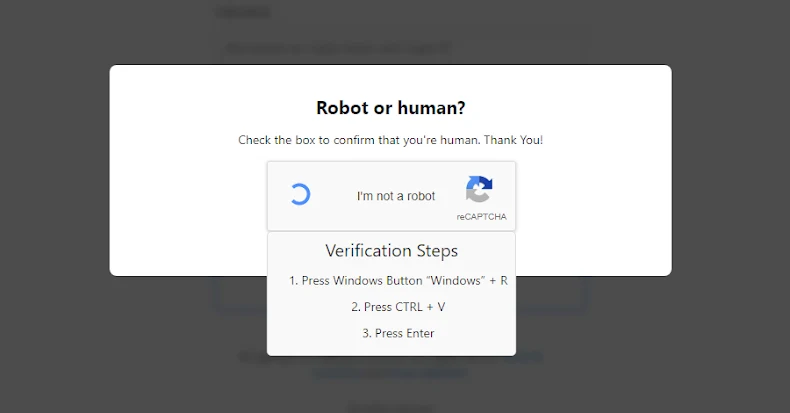
As cyberattacks become more prevalent and sophisticated, traditional approaches characterized by siloed identity tools can’t keep pace with evolving threats. Today’s rapidly expanding attack surface is driven primarily by non-human identities (NHIs), including service accounts, API keys, and AI agents.
Fragmented point solutions weaken an organization’s overall security posture, increase operational complexity, and elevate risk due to inconsistent configurations and limited threat visibility. This fragmentation leads to inefficiency as security and IT teams struggle with disjointed workflows.
Critical drivers for adoption:
Key benefits of identity security fabric:
- Unifies visibility and control: Provides security teams with a centralized control plane for unified insight and consistent policy enforcement across the entire identity surface
- Secures all identities at scale: Protects human users and NHIs, including machine accounts and emerging AI agents, with consistent governance rigor
- Enables continuous, risk-aware access: Supports the Zero Trust model by implementing adaptive, real-time access controls based on continuous risk assessment
- Streamlines access and governance: Automates and simplifies identity lifecycle management to improve security, ensure compliance, and reduce operational complexity
Core principles of an identity security fabric
The design principles of identity security fabric center on creating a seamless and secure UX, reducing complexity, ensuring compliance, and enabling AI-driven modernization by connecting people, processes, and technology through an identity-first approach.
The ten fundamental elements that guide an identity fabric architecture, according to Tech Republic’s summary of Gartner’s identity fabric principles.
- Any human or machine
- Centralized control and decentralized enablement
- Composed, orchestrated, and journey-oriented architecture
- Adaptive, continuous, risk-aware, and resilient security
- Pervasive standards
- Event-based integration connectivity
- Continuous and automated change
- Prescriptive and remediating threat detection and response
- Privacy for everyone
- Continuous observability
How identity security fabric works: The multi-layer architecture
ISF uses a multi-layer, vendor-neutral architecture that enables organizations to build upon cohesive identity and access management (IAM) capabilities, real-time risk-aware access controls, and seamless integration.
Layer 1: Integrated identity security capabilities
This layer extends beyond basic authentication to encompass all critical security functions for the identity lifecycle:
- Identity security posture management (ISPM): Continuous monitoring to detect anomalies, enforce AI policies, and maintain audit readiness for autonomous agents, workloads, and high-risk identities
- Identity governance and administration (IGA): Entitlement reviews, access certification, and policy management to enforce least privilege
- Privileged access management (PAM): High-risk account controls, just-in-time (JIT) access, and administrative function protection
- Access management: Provisioning, single sign-on (SSO), federation, and strong authentication across all applications
- Identity threat protection: Behavioral analytics, anomaly detection, automated response, and real-time risk assessment
Protection throughout the identity lifecycle
An effective identity security fabric protects before, during, and after authentication:
| Protection Phase |
Capabilities |
Purpose |
| Before authentication |
IGA, ISPM, PAM, lifecycle management |
Ensure only authorized identities exist with appropriate, least privileges |
| During authentication |
Adaptive authentication, multifactor authentication (MFA), and access controls |
Verify identity and make a real-time, risk-based access decision |
| After authentication |
ITDR, continuous monitoring, behavioral analytics |
Detect anomalies, enforce session controls, and respond to threats in real time |
Layer 2: Identity orchestration
Orchestration is the critical layer that transforms disconnected IAM tools into a true fabric, enabling real-time threat prevention and response.
KuppingerCole defines orchestration as a core component of identity fabrics, highlighting its role in connecting existing investments with newer, specialized capabilities to incrementally reduce technical debt.
Key orchestration functions:
- Seamless data exchange: Automated real-time sharing of identity data, access decisions, and risk signals across IAM components
- Workflow automation: Coordinated execution of identity-driven processes (e.g., user onboarding, security incident response) across multiple systems without manual handoffs
- Policy coordination: Consistent enforcement of security policies across every environment and application
- Event-driven responses: Automated, enterprise-wide reactions when threats are detected. (e.g., immediate session revocation across all systems when credentials are compromised)
Layer 3: Comprehensive integrations
Identity security fabric must extend across the entire technology stack. Deep, bidirectional integrations connect every identity to every resource, eliminating the silos that create security gaps and enabling consistent policy enforcement everywhere.
Through standardized integrations built on open protocols (SAML, OAuth, OIDC, SCIM, LDAP), the fabric accommodates the multi-vendor reality, enabling organizations to adopt best-of-breed tools as needed.
Integration scope: Weaving the fabric across the enterprise
Identity fabric effectiveness depends on its ability to enforce policy across four key domains:
| Integration Domain |
Technical Value and Alignment |
| Infrastructure |
Connections to cloud infrastructure platforms (IaaS) and on-premises services enable consistent identity governance whether workloads run in public clouds, private data centers, or hybrid environments.
This ensures unified access across virtualization platforms, container environments, and traditional server infrastructure, directly supporting Cloud Infrastructure Entitlement Management (CIEM) principles.
|
| Applications |
Support for cloud-native applications and on-premises software through standard protocols (SAML, OAuth, OIDC, SCIM) and custom connectors.
ISF integrates with SaaS platforms, internally developed applications, packaged enterprise software, and legacy systems without requiring application rewrites.
|
| APIs |
Bi-directional integration with public-facing and internal APIs enables programmatic identity management, automated workflows, and secure machine-to-machine authentication.
Standard API protocols ensure that services can authenticate and authorize programmatically while maintaining security controls—essential for the DevOps pipeline.
|
| Identities |
Integration with enterprise directories, identity providers, and identity sources provides complete visibility into all identity types.
This includes human users (managed through directory services), as well as machine identities, workload identities, and AI agents that require the same governance rigor as human accounts.
|
The multi-vendor reality
By embracing a composable architecture that relies on open protocols, the identity security fabric enables organizations to successfully unify their IAM infrastructure, even when components are sourced from multiple vendors. This approach reduces risk, avoids vendor lock-in, and provides strategic flexibility to integrate specialized security capabilities (such as IGA or PAM) without compromising the unified security architecture. This vendor-agnostic extensibility is a core mandate of the overall identity fabric concept.
Benefits of identity security fabric
Adopting an identity security fabric delivers security and business advantages, aligning enterprise resilience with digital transformation and AI adoption goals.
Security benefits
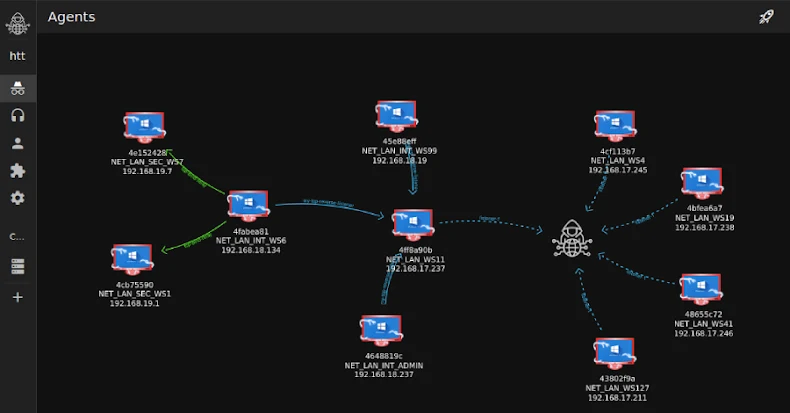
- Stronger protection against credential theft, privilege misuse, and lateral movement: By making identity the primary control plane, enterprises contain risk at the source for humans, machines, and AI agents
- Complete visibility across all identities: A unified view of human users, service accounts, workloads, API keys, and autonomous agents reduces blind spots and accelerates threat detection
- Automated threat detection and response for AI and non-human entities: Continuous monitoring identifies anomalies in behavior, access patterns, or autonomous workflows, enabling rapid mitigation
- AI governance and audit readiness: Every action by autonomous systems is traceable, policy-compliant, and auditable, supporting regulatory frameworks and enterprise trust
- Comprehensive orchestration to prevent, detect, and stop threats: Unified response capabilities across the entire identity attack surface
Business advantages
- Enhanced operational agility: Securely adopt cloud services, expand SaaS usage, and integrate AI-driven workflows without compromising compliance or productivity
- Improved UX and developer experience: Seamless adaptive authentication, passwordless access, and consistent identity policies reduce friction across human and machine workflows
- Regulatory and compliance readiness: Centralized governance and reporting simplify audits for frameworks such as NIST, ISO 27001, SOC 2, GDPR, and emerging AI-specific standards
- Identity-focused AI analytics and insights: Observability and analytics capabilities provide actionable insights into autonomous systems, helping optimize AI deployment and risk management
Identity security fabric use cases
ISF weaves security into every identity from end-to-end:
- Securing AI agents: As AI agents become integral to the workforce, they introduce new identity and access challenges. ISF provides the visibility to discover and assess risky agents, centralized controls to manage and restrict access, and automated governance to enforce security policies and oversee each agent’s lifecycle.
- Protecting non-human identities: Modern applications and automation increasingly depend on non-human identities, like service accounts. A strong identity security fabric ensures that these identities are appropriately managed, secured, and governed, just like human users, closing a crucial and frequently overlooked security gap.
- Securing hybrid and on-premises environments: Many organizations continue to rely on legacy and on-premises systems. An ISF extends identity governance, threat protection, and access management across hybrid and on-prem environments. This approach helps proactively identify and mitigate directory vulnerabilities, maintain resilient access even when offline, and automate threat responses.
- Enabling security-driven governance: Identity governance is often treated as a compliance requirement rather than a security capability. Within an identity security fabric, governance becomes an active defense layer enabling least privilege enforcement and risk-based access certifications that reduce exposure and improve resilience.
- Securing workforce onboarding: The onboarding experience sets the foundation for workforce security. An ISF can automate and secure this process from the moment a new identity is created, using phishing-resistant authentication and adaptive access controls to ensure every user starts with the right permissions from the start.
Regulatory compliance for the AI era
A unified identity security fabric provides the foundational evidence required for both traditional and emerging regulatory frameworks.
Traditional compliance
Centralized policy management and consistent logging simplify audits for frameworks like NIST, ISO 27001, SOC 2, and GDPR. The IGA component ensures provable compliance with the principle of least privilege and provides comprehensive access certification records for human and non-human identities.
AI-specific mandates
The fabric is essential in preparing for new global standards, like the EU AI Act and the NIST AI Risk Management Framework. These regulations require strict accountability, explainability, and auditability for automated systems.
ISF solves this by:
- Assigning a verifiable identity (a “first-class citizen”) to every AI agent
- Using standards like the Cross-App Access (XAA) protocol to centrally control and log every agent-to-app action
- Ensuring the centralized identity graph contains the full context of who (or what) performed an action, when, and why, is crucial for maintaining regulatory trust and managing the challenges associated with high-risk AI systems
The future of identity: Self-healing architectures
As AI systems proliferate, NHIs far outnumber human users. Identity security fabric must evolve into self-healing architectures, where AI-driven analytics detect anomalies, enforce policies, and adapt to new risks in real time.
Emerging capabilities
- Agentic AI governance: Sophisticated delegation and oversight for autonomous AI systems
- Identity-as-a-mesh: A scalable, independent identity architecture that surrounds the organization
- Autonomous policy adaptation: Using machine learning (ML) to adjust security controls to new threat vectors automatically
Organizations that implement identity security fabric now are better positioned to thrive in an AI-native, regulation-heavy, and constantly evolving digital landscape.
FAQs
How does Identity Security Fabric differ from traditional IAM?
IAM often manages access in silos. Identity security fabric integrates IAM, governance, and adaptive authentication into a continuous, unified identity-centric control plane that spans hybrid environments, including both human and AI agents.
Is Identity Security Fabric the same as Zero Trust?
No. Zero Trust is a security model (never trust, always verify). Identity security fabric is the architectural foundation and set of enabling technologies that enforces identity-driven policies to make Zero Trust possible across all access decisions.
Does Identity Security Fabric cover non-human identities?
Yes. It governs service accounts, workloads, APIs, and AI agents, ensuring that NHIs follow the same least-privilege and compliance requirements as human users.
How does identity security fabric relate to cybersecurity mesh architecture (CSMA)?
Cybersecurity mesh, a term coined by Gartner, is a collaborative environment of tools and controls designed to secure a distributed enterprise. Identity security fabric is the specialized, identity-centric control plane that enforces consistent, adaptive policies for all identities (human and machine) across the entire mesh, which is essential for Zero Trust enablement.
Turn identity into your strongest defense
Discover how the Okta Platform empowers organizations to build a comprehensive identity security fabric that seamlessly unifies access control, threat detection and response, and governance, providing a single layer of defense.
Learn more
Found this article interesting?
This article is a contributed piece from one of our valued partners. Follow us on
Google News,
Twitter and
LinkedIn to read more exclusive content we post.