Dozens of organizations may have been impacted following the zero-day exploitation of a security flaw in Oracle’s E-Business Suite (EBS) software since August 9, 2025, Google Threat Intelligence Group (GTIG) and Mandiant said in a new report released Thursday.
“We’re still assessing the scope of this incident, but we believe it affected dozens of organizations,” John Hultquist, chief analyst of GTIG at Google Cloud, said in a statement shared with The Hacker News. “Some historic Cl0p data extortion campaigns have had hundreds of victims. Unfortunately, large-scale zero-day campaigns like this are becoming a regular feature of cybercrime.”
The activity, which bears some hallmarks associated with the Cl0p ransomware crew, is assessed to have fashioned together multiple distinct vulnerabilities, including a zero-day flaw tracked as CVE-2025-61882 (CVSS score: 9.8), to breach target networks and exfiltrate sensitive data. Google said it found evidence of additional suspicious activity dating back to July 10, 2025, although how successful these efforts were remains unknown. Oracle has since issued patches to address the shortcoming.
Cl0p (aka Graceful Spider), active since 2020, has been attributed to the mass exploitation of several zero-days in Accellion legacy file transfer appliance (FTA), GoAnywhere MFT, Progress MOVEit MFT, and Cleo LexiCom over the years. While phishing email campaigns undertaken by the FIN11 actors have acted as a precursor for Cl0p ransomware deployment in the past, Google said it found signs of the file-encrypting malware being a different actor.
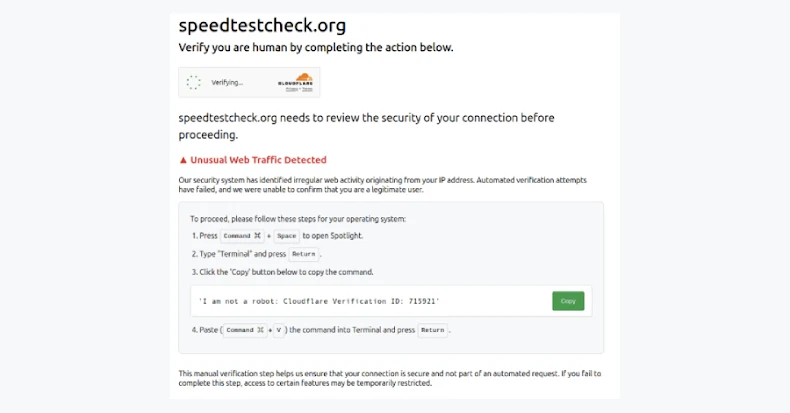
The latest wave of attacks began in earnest on September 29, 2025, when the threat actors kicked off a high-volume email campaign aimed at company executives from hundreds of compromised third-party accounts belonging to unrelated organizations. The credentials for these accounts are said to have been purchased on underground forums, presumably through the purchase of infostealer malware logs.
The email messages claimed the actor had breached their Oracle EBS application and exfiltrated sensitive data, demanding that they pay an unspecified amount as ransom in return for not leaking the stolen information. To date, none of the victims of the campaign have been listed on the Cl0p data leak site – a behavior that’s consistent with prior Cl0p attacks where the actors waited for several weeks before posting them.
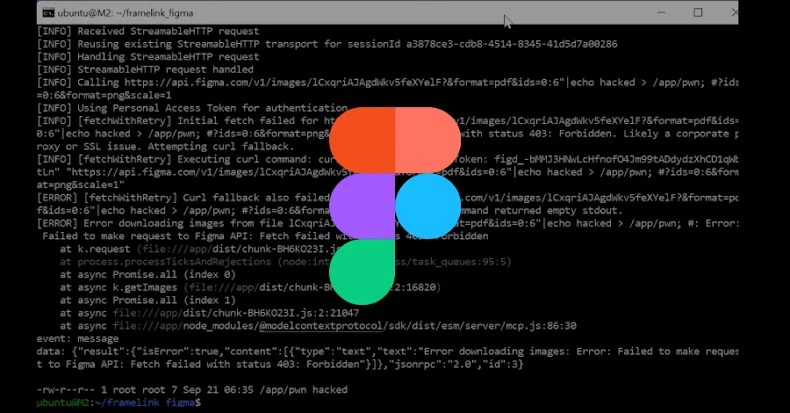
The attacks themselves leverage a combination of Server-Side Request Forgery (SSRF), Carriage-Return Line-Feed (CRLF) injection, authentication bypass, and XSL template injection, to gain remote code execution on the target Oracle EBS server and set up a reverse shell.
Sometime around August 2025, Google said it observed a threat actor exploiting a vulnerability in the “/OA_HTML/SyncServlet” component to achieve remote code execution and ultimately trigger an XSL payload via the Template Preview functionality. Two different chains of Java payloads have been found embedded in the XSL payloads –
- GOLDVEIN.JAVA, a Java variant of a downloader called GOLDVEIN (a PowerShell malware first detected in December 2024 in connection with the exploitation campaign of multiple Cleo software products) that can receive a second-stage payload from a command-and-control (C2) server.
- A Base64-encoded loader called SAGEGIFT custom designed for Oracle WebLogic servers that’s used to launch SAGELEAF, an in-memory dropper that’s then used to install SAGEWAVE, a malicious Java servlet filter that allows for the installation of an encrypted ZIP archive containing an unknown next-stage malware. (The main payload, however, has some overlaps with a cli module present in a FIN11 backdoor known as GOLDTOMB.)
The threat actor has also been observed executing various reconnaissance commands from the EBS account “applmgr,” as well as running commands from a bash process launched from a Java process running GOLDVEIN.JAVA.
Interestingly, some of the artifacts observed in July 2025 as part of incident response efforts overlap with an exploit leaked in a Telegram group named Scattered LAPSUS$ Hunters on October 3, 2025. However, Google said it does not have sufficient evidence to suggest any involvement of the cybercrime crew in the campaign.
The level of investment into the campaign suggests the threat actors responsible for the initial intrusion likely dedicated significant resources to pre-attack research, GTIG pointed out.
The tech giant said it’s not formally attributing the attack spree to a tracked threat group, although it pointed out the use of the Cl0p brand as notable. That said, it’s believed that the threat actor has an association with Cl0p. It also noted that the post-exploitation tooling exhibits overlaps with malware (i.e., GOLDVEIN and GOLDTOMB) used in a previous suspected FIN11 campaign, and that one of the breached accounts used to send the recent extortion emails was previously used by FIN11.
“The pattern of exploiting a zero-day vulnerability in a widely used enterprise application, followed by a large-scale, branded extortion campaign weeks later, is a hallmark of activity historically attributed to FIN11 that has strategic benefits which may also appeal to other threat actors,” it said.
“Targeting public-facing applications and appliances that store sensitive data likely increases the efficiency of data theft operations, given that the threat actors do not need to dedicate time and resources to lateral movement.”
Source: thehackernews.com…