Cybersecurity researchers have discovered over a dozen vulnerabilities in enterprise secure vaults from CyberArk and HashiCorp that, if successfully exploited, can allow remote attackers to crack open corporate identity systems and extract enterprise secrets and tokens from them.
The 14 vulnerabilities, collectively named Vault Fault, affect CyberArk Secrets Manager, Self-Hosted, and Conjur Open Source and HashiCorp Vault, according to a report from an identity security firm Cyata. Following responsible disclosure in May 2025, the flaws have been addressed in the following versions –
These include authentication bypasses, impersonation, privilege escalation bugs, code execution pathways, and root token theft. The most severe of the issues allows for remote code execution, allowing attackers to takeover the vault under certain conditions without any valid credentials –
- CVE-2025-49827 (CVSS score: 9.1) – Bypass of IAM authenticator in CyberArk Secrets Manager
- CVE-2025-49831 (CVSS score: 9.1) – Bypass of IAM authenticator in CyberArk Secrets Manager via a misconfigured network device
- CVE-2025-49828 (CVSS score: 8.6) – Remote code execution in CyberArk Secrets Manager
- CVE-2025-6000 (CVSS score: 9.1) – Arbitrary remote code execution via plugin catalog abuse in HashiCorp Vault
- CVE-2025-5999 (CVSS score: 7.2) – Privilege escalation to root via policy normalization in HashiCorp Vault
In addition, vulnerabilities have also been discovered in HashiCorp Vault’s lockout protection logic, which is designed to throttle brute-force attempts, that could permit an attacker to infer which usernames are valid by taking advantage of a timing-based side channel and even reset the lockout counter by changing the case of a known username (e.g., admin to Admin).
Two other shortcomings identified by the Israeli company made it possible to weaken lockout enforcement and bypass multi-factor authentication (MFA) controls when username_as_alias=true in the LDAP auth configuration and MFA enforcement is applied at the EntityID or IdentityGroup level.
In the attack chain detailed by the cybersecurity company, it’s possible to leverage a certificate entity impersonation issue (CVE-2025-6037) with CVE-2025-5999 and CVE-2025-6000 to break the authentication layer, escalate privileges, and achieve code execution. CVE-2025-6037 and CVE-2025-6000 are said to have existed for over eight and nine years, respectively.
Armed with this capability, a threat actor could further weaponize the access to delete the “core/hsm/_barrier-unseal-keys” file, effectively turning a security feature into a ransomware vector. What’s more, the Control Group feature can be undermined to send HTTP requests and receive responses without being audited, creating a stealthy communication channel.
“This research shows how authentication, policy enforcement, and plugin execution can all be subverted through logic bugs, without touching memory, triggering crashes, or breaking cryptography,” security researcher Yarden Porat said.
In a similar vein, the vulnerabilities discovered in CyberArk Secrets Manager/Conjur allow for authentication bypass, privilege escalation, information disclosure, and arbitrary code execution, effectively opening the door to a scenario where an attacker can craft an exploit chain to obtain unauthenticated access and run arbitrary commands.
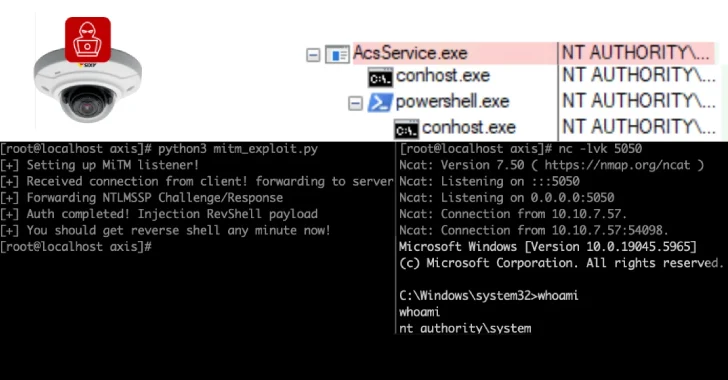
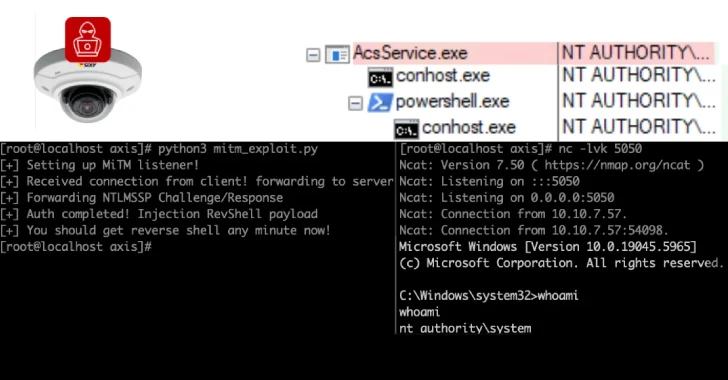
The attack sequence unfolds as follows –
- IAM authentication bypass by forging valid-looking GetCallerIdentity responses
- Authenticate as a policy resource
- Abuse the Host Factory endpoint to create a new host that impersonates a valid policy template
- Assigned a malicious Embedded Ruby (ERB) payload directly to the host
- Trigger the execution of the attached ERB by invoking the Policy Factory endpoint
“This exploit chain moved from unauthenticated access to full remote code execution without ever supplying a password, token, or AWS credentials,” Porat noted.
The disclosure comes as Cisco Talos detailed security flaws in Dell’s ControlVault3 Firmware and its associated Windows APIs that could have been abused by attackers to bypass Windows login, extract cryptographic keys, as well as maintain access even after a fresh operating system install by deploying undetectable malicious implants into the firmware.
Together, these vulnerabilities create a potent remote post-compromise persistence method for covert access to high-value environments. The identified vulnerabilities are as follows –
- CVE-2025-25050 (CVSS score: 8.8) – An out-of-bounds write vulnerability exists in the cv_upgrade_sensor_firmware functionality that could lead to an out-of-bounds write
- CVE-2025-25215 (CVSS score: 8.8) – An arbitrary free vulnerability exists in the cv_close functionality that could lead to an arbitrary free
- CVE-2025-24922 (CVSS score: 8.8) – A stack-based buffer overflow vulnerability exists in the securebio_identify functionality that could lead to arbitrary code execution
- CVE-2025-24311 (CVSS score: 8.4) – An out-of-bounds read vulnerability exists in the cv_send_blockdata functionality that could lead to an information leak
- CVE-2025-24919 (CVSS score: 8.1) – A deserialization of untrusted input vulnerability exists in the cvhDecapsulateCmd functionality that could lead to arbitrary code execution
The vulnerabilities have been codenamed ReVault. More than 100 models of Dell laptops running Broadcom BCM5820X series chips are affected. There is no evidence that the vulnerabilities have been exploited in the wild.
The cybersecurity company also pointed out that a local attacker with physical access to a user’s laptop could pry it open and access the Unified Security Hub (USH) board, allowing an attacker to exploit any of the five vulnerabilities without having to log in or possess a full-disk encryption password.
“The ReVault attack can be used as a post-compromise persistence technique that can remain even across Windows reinstalls,” Cisco Talos researcher Philippe Laulheret said. “The ReVault attack can also be used as a physical compromise to bypass Windows Login and/or for any local user to gain Admin/System privileges.”
To mitigate the risk posed by these flaws, users are advised to apply the fixes provided by Dell; disable ControlVault services if peripherals like fingerprint readers, smart card readers, and near-field communication (NFC) readers are not being used; and turn off fingerprint login in high-risk situations.
Source: thehackernews.com…