The Latest
-
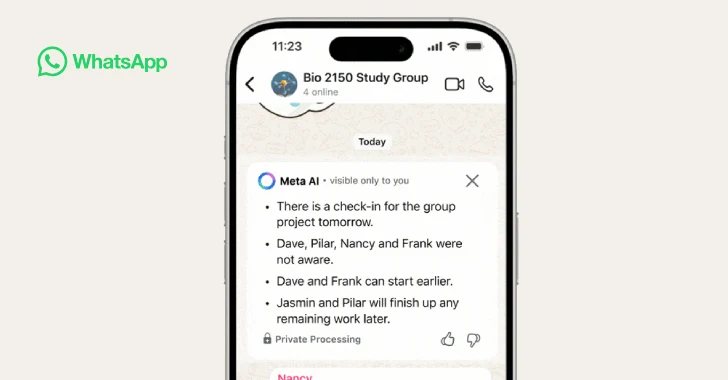
WhatsApp Adds AI-Powered Message Summaries for Faster Chat Previews
-
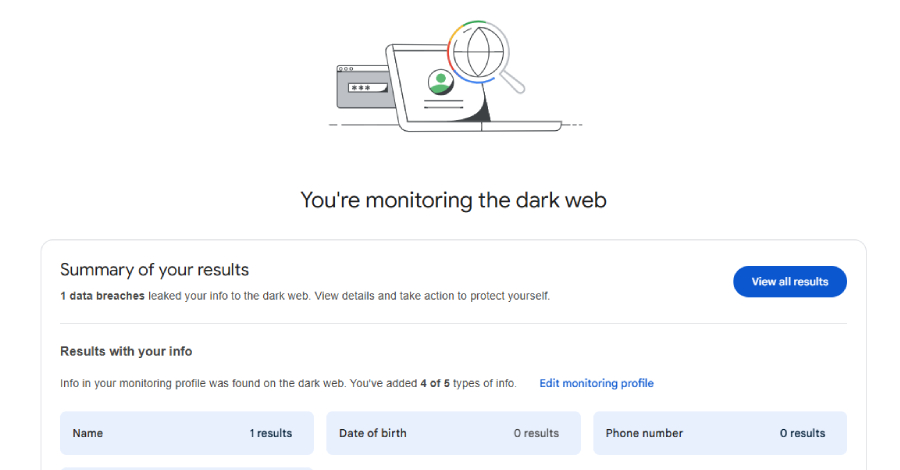
nOAuth Vulnerability Still Affects 9% of Microsoft Entra SaaS Apps Two Years After Discovery
-
Citrix Releases Emergency Patches for Actively Exploited CVE-2025-6543 in NetScaler ADC
-
Citrix Bleed 2 Flaw Enables Token Theft; SAP GUI Flaws Risk Sensitive Data Exposure