The Latest
-
Chinese Group Silver Fox Uses Fake Websites to Deliver Sainbox RAT and Hidden Rootkit
-
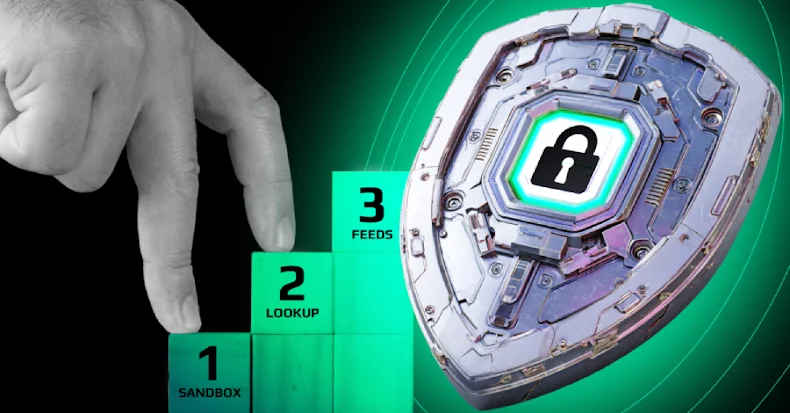
Business Case for Agentic AI SOC Analysts
-
MOVEit Transfer Faces Increased Threats as Scanning Surges and CVE Flaws Are Targeted
-
OneClik Malware Targets Energy Sector Using Microsoft ClickOnce and Golang Backdoors