The Latest
-
North Korean Hackers Deploy 197 npm Packages to Spread Updated OtterCookie Malware
-
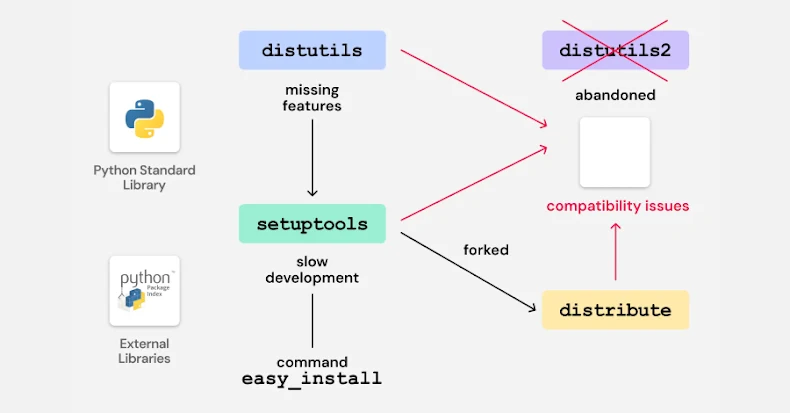
Legacy Python Bootstrap Scripts Create Domain-Takeover Risk in Multiple PyPI Packages
-
Why Organizations Are Turning to RPAM
-
MS Teams Guest Access Can Remove Defender Protection When Users Join External Tenants