The Latest
-
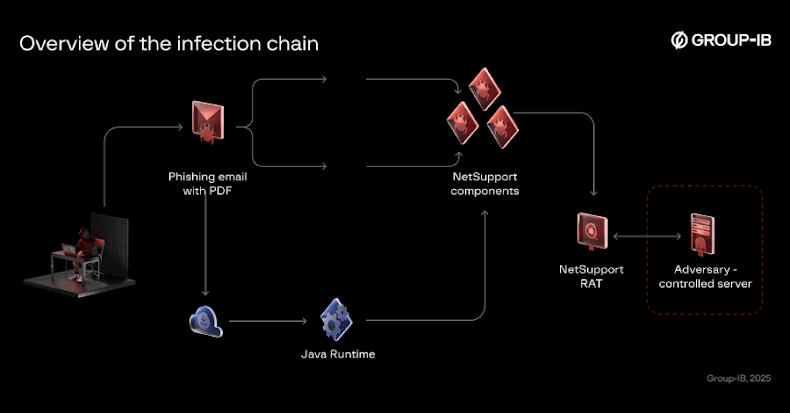
Bloody Wolf Expands Java-based NetSupport RAT Attacks in Kyrgyzstan and Uzbekistan
-
Microsoft to Block Unauthorized Scripts in Entra ID Logins with 2026 CSP Update
-
ThreatsDay Bulletin: AI Malware, Voice Bot Flaws, Crypto Laundering, IoT Attacks — and 20 More Stories
-
Gainsight Expands Impacted Customer List Following Salesforce Security Alert