The Latest
-
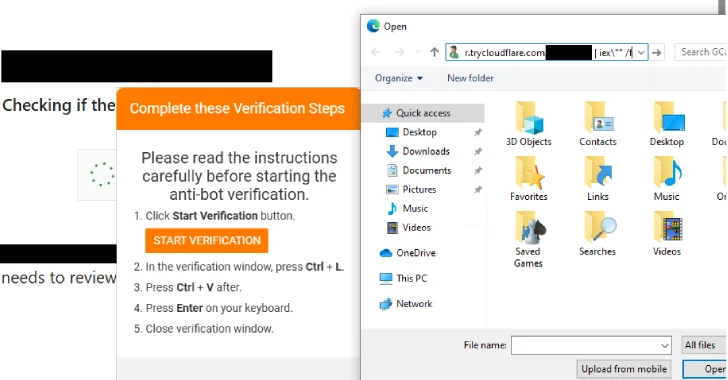
New PHP-Based Interlock RAT Variant Uses FileFix Delivery Mechanism to Target Multiple Industries
-
The Unusual Suspect: Git Repos
-
⚡ Weekly Recap: Scattered Spider Arrests, Car Exploits, macOS Malware, Fortinet RCE and More
-
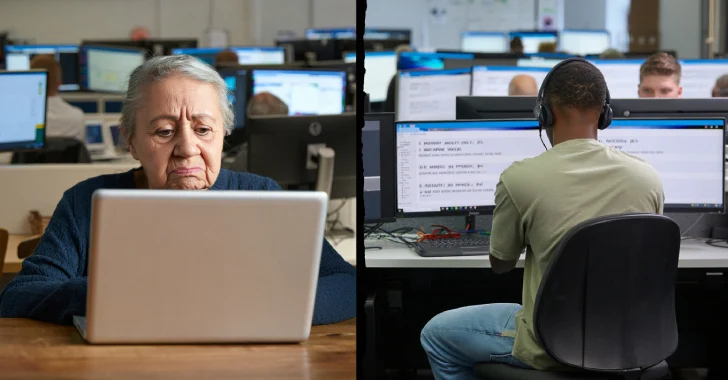
CBI Shuts Down £390K U.K. Tech Support Scam, Arrests Key Operatives in Noida Call Center